Acl Diagram
Get Acl Diagram Pics. Configure remote access vpn (ipsec). An intranet should be heavily protected by different networking devices, such as router, firewall, proxy server, honeynet, ips and ids.
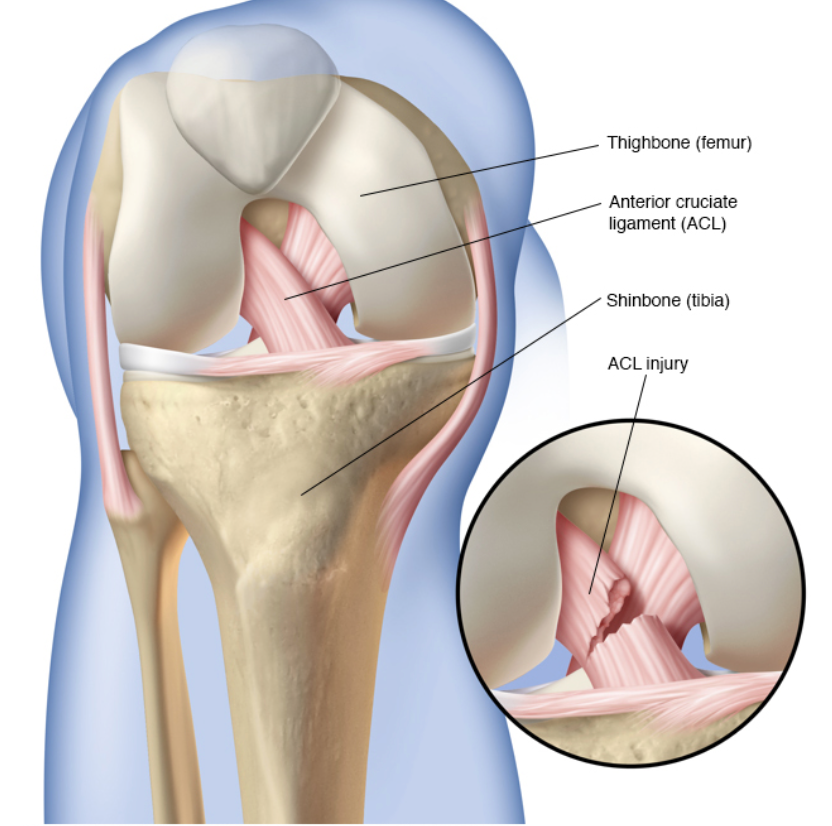
In this image, you will find damaged acl is removed and a notch is drilled into the distal femur., incision is made in the knee from the patella to the proximal tibia., drill holes are made into the tibia and the femur, the graft is pulled through the holes and secure into.
Ip acls operate on layers 3 and 4. In this way, acl helps to limit network traffic, manage network access behaviors, forward packets to specified ports and more. Ip acls operate on layers 3 and 4. In this image, you will find damaged acl is removed and a notch is drilled into the distal femur., incision is made in the knee from the patella to the proximal tibia., drill holes are made into the tibia and the femur, the graft is pulled through the holes and secure into.
0 Response to "Acl Diagram"
Post a Comment